A Dramatic Shift in Network Security with Zero Trust Edge Strategy
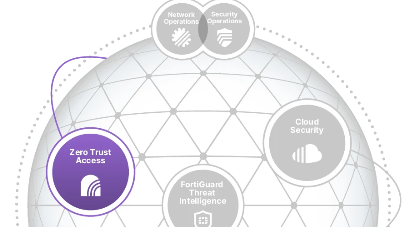
This strategy simplifies the protection of the expanding attack surface regardless of where users or devices are located.
Consistent convergence of networking and security across all edges - Free Whitepaper Download!


A security-driven networking strategy tightly integrates an organization’s network infrastructure and security architecture, enabling the network to scale and change without compromising security operations. It is critical to have this convergence available on-premises and in the cloud to secure all networks and users.
Get your copy of the comprehensive Zero Trust Edge Strategy Whitepaper, that covers:
- WAN Edge Modernization
- Security Integration at the LAN Edge
- Consistent Protection Throughout the Network
- Automation With Centralized Management and Analytics
Overview:
Digital acceleration has created a perfect storm of complexity for IT and cybersecurity teams, especially when they are being asked to also meet their organization’s mandate to maintain high performance and optimal user experience. Security-driven networking relieves the burden on IT teams by converging security and networking. It simplifies operational management, provides better security, and enables broad visibility across all network edges. These key steps are essential in building a long-term zero trust edge strategy.
Learn About:
- What Zero Trust Edge is
- What Strategies to Employ
- What Converged Security and Networking Does
- WAN Edge Modernization
- Automation with Centralized Management
“By 2024, to increase agility and enhance support for cloud applications, 60% of enterprises will have implemented SD-WAN — up from less than 20% today."